With fines for non-compliance of up to 4% of a company’s annual global turnover or €20 Million (whichever is greater), and applicable regardless of the company’s location (i.e.: Mauritius). GDPR is a regulation that can no longer be ignored from any companies processing personal data of EU Residents (i.e.: travel agencies, hospitality, banking, health care, insurance, etc.).
This article provides key facts as well as some resources to get started on the road to GDPR compliance.
---
1. Key facts about GDPR;
2. Relevant Definitions;
3. The route to GDPR compliance;
4. Going further.
---
1 - Key facts about GDPR
>>[READ MORE]

 GDPR and what it means to companies in the Indian Ocean and Africa
GDPR and what it means to companies in the Indian Ocean and Africa
 Are Cyber Security Challenges and Opportunities in Mauritius and Africa different from Europe?
Are Cyber Security Challenges and Opportunities in Mauritius and Africa different from Europe?
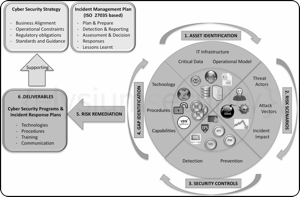 Cyber Security Planning - A simple 6 Steps Approach
Cyber Security Planning - A simple 6 Steps Approach
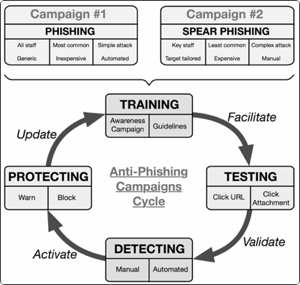 How to build an efficient Anti-Phishing Framework?
How to build an efficient Anti-Phishing Framework?